8.5. Prevention
 There are a number of ways to prevent unauthorized access, or loss including: access controls, encryption, firewalls, antivirus programs, and backups.
There are a number of ways to prevent unauthorized access, or loss including: access controls, encryption, firewalls, antivirus programs, and backups.
Access Control
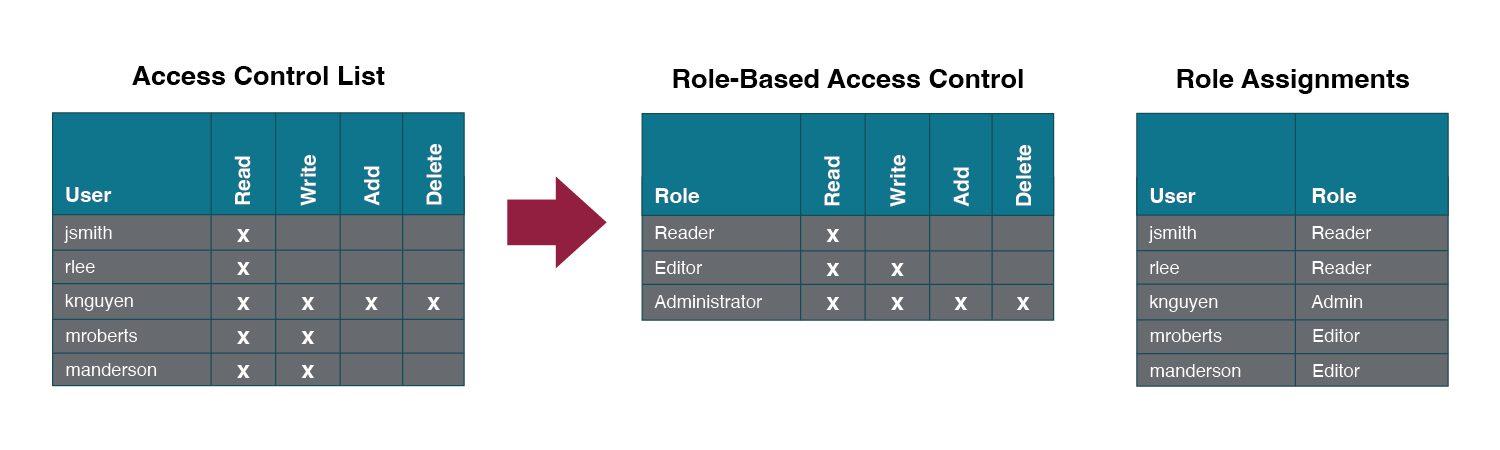
Once a user has been authenticated, the next step is to ensure that they can only access the information resources that are appropriate. This is done through the use of access control. Access control determines which users are authorized to read, modify, add, and or delete information. Several different access control models exist. Two of the more common are: the Access Control List (ACL) and Role-Based Access Control (RBAC).
An information security employee can produce an ACL which identifies a list of users who have the capability to take specific actions with an information resource such as data files. Specific permissions are assigned to each user such as read, write, delete, or add. Only users with those permissions are allowed to perform those functions.
ACLs are simple to understand and maintain, but there are several drawbacks. The primary drawback is that each information resource is managed separately, so if a security administrator wanted to add or remove a user to a large set of information resources, it would be quite difficult. And as the number of users and resources increase, ACLs become harder to maintain. This has led to an improved method of access control, called role-based access control, or RBAC. With RBAC, instead of giving specific users access rights to an information resource, users are assigned to roles and then those roles are assigned the access. This allows the administrators to manage users and roles separately, simplifying administration and, by extension, improving security.
The following image shows an ACL with permissions granted to individual users. RBAC allows permissions to be assigned to roles, as shown in the middle grid, and then in the third grid each user is assigned a role. Although not modeled in the image, each user can have multiple roles such as Reader and Editor.
Encryption
Many times an organization needs to transmit information over the Internet or transfer it on external media such as a flash drive. In these cases, even with proper authentication and access control, it is possible for an unauthorized person to gain access to the data. Encryption scrambles data so that it is unreadable to those without a public key, which unlocks or decrypts the data. This is referred to as symmetric key encryption where both parties share the encryption key. Encryption makes information secure as the message is sent in code and appears to those without the public key as a random series of letters and numbers.
An alternative to symmetric key encryption is public key encryption. In public key encryption, two keys are used: a public key and a private key. To send an encrypted message, you obtain the public key, encode the message, and send it. The recipient then uses their private key to decode it. The public key can be given to anyone who wishes to send the recipient a message. Each user simply needs one private key and one public key in order to secure messages. The private key is necessary in order to decrypt a message sent with the public key.
Notice in the image how the sender on the left creates a plaintext message which is then encrypted with a public key. The ciphered text is transmitted through the communication channel and the recipient uses their private key to decrypt the message and then read the plain text.
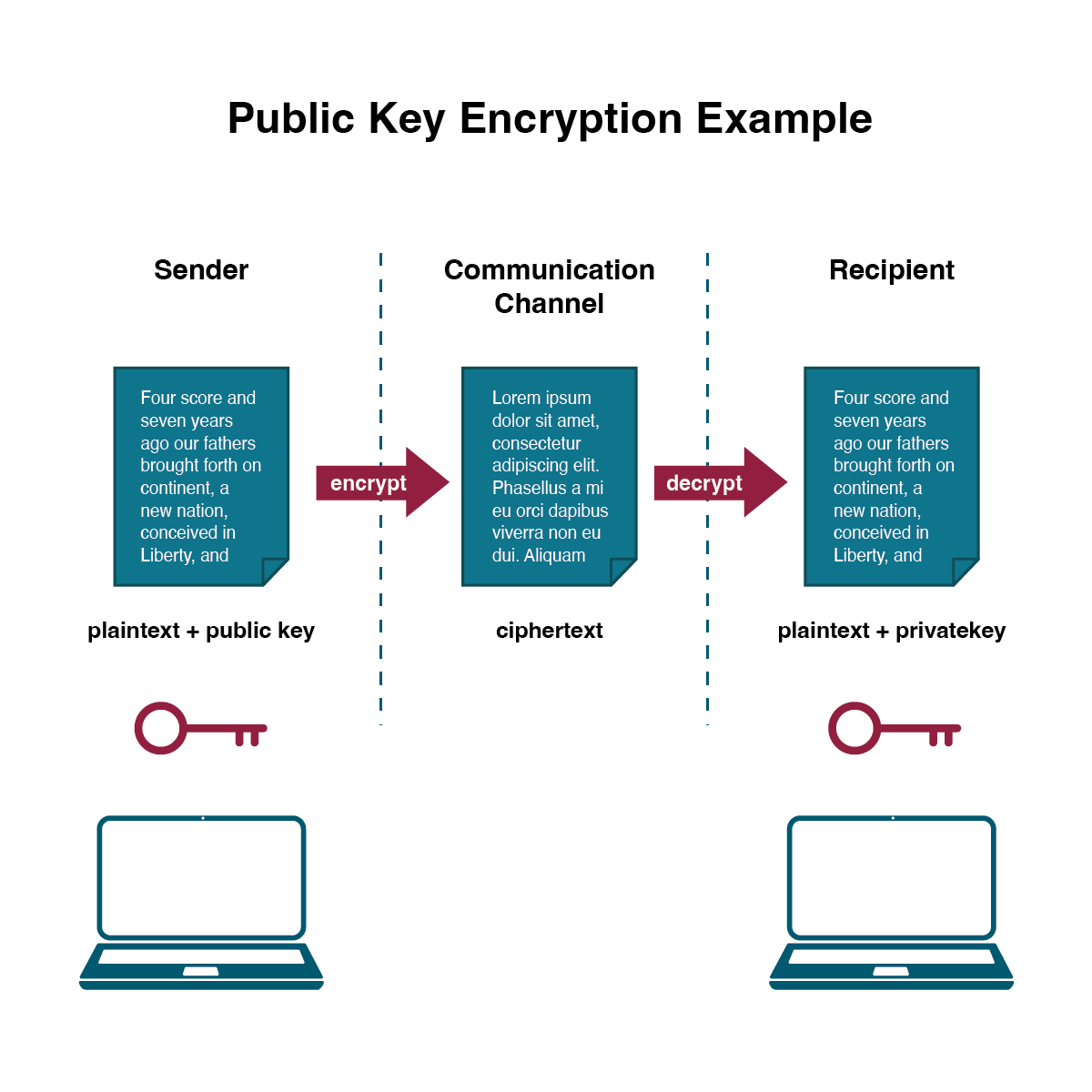
Public Key Encryption – The ciphered text is transmitted through the communication channel and the recipient uses their private key to decrypt the message and then read the plain text. (click to enlarge). Adapted from D. Bourgeois CC-BY-NC
Firewalls
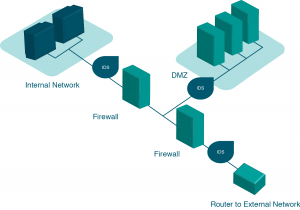
Firewalls are another method that an organization can use for increasing security on its network. A firewall can exist as hardware or software, or both. A hardware firewall is a device that is connected to the network and filters the packets based on a set of rules. One example of these rules would be preventing packets entering the local network that come from unauthorized users. A software firewall runs on the operating system and intercepts packets as they arrive at a computer.
A firewall protects all company servers and computers by stopping packets from outside the organization’s network that do not meet a strict set of criteria. A firewall may also be configured to restrict the flow of packets leaving the organization. This may be done to eliminate the possibility of employees watching YouTube videos or using Facebook from a company computer. A VPN allows a user who is outside of a corporate network to take a detour around the firewall and access the internal network from the outside. Through a combination of software and security measures, a VPN provides off-site access to the organization’s network while ensuring overall security.
Anti-virus Programs
Antivirus programs are software that can be installed on a computer or network to detect and remove known malicious programs like viruses, and spyware. While antivirus programs provide some protection they are a reactive defense in that they must first understand what to look for.
Backups
Another essential tool for information security is a comprehensive backup plan for the entire organization. Not only should the data on the corporate servers be backed up, but individual computers used throughout the organization should also be backed up. A good backup plan should consist of several components.
- Full understanding of the organization’s information resources. What information does the organization actually have? Where is it stored? Some data may be stored on the organization’s servers, other data on users’ hard drives, some in the cloud, and some on third-party sites. An organization should make a full inventory of all of the information that needs to be backed up and determine the best way to back it up.
- Regular backups of all data. The frequency of backups should be based on how important the data is to the company, combined with the ability of the company to replace any data that is lost. Critical data should be backed up daily, while less critical data could be backed up weekly. Most large organizations today use data redundancy so their records are always backed up.
- Offsite storage of backup data sets. If all backed-up data is being stored in the same facility as the original copies of the data, then a single event such as an earthquake, fire, or tornado would destroy both the original data and the backup. It is essential the backup plan includes storing the data in an offsite location.
- Test of data restoration. Backups should be tested on a regular basis by having test data deleted then restored from backup. This will ensure that the process is working and will give the organization confidence in the backup plan.
Besides these considerations, organizations should also examine their operations to determine what effect downtime would have on their business. If their information technology were to be unavailable for any sustained period of time, how would it impact the business?
Additional concepts related to backup include the following:
- Uninterruptible Power Supply (UPS). A UPS provides battery backup to critical components of the system, allowing them to stay online longer and/or allowing the IT staff to shut them down using proper procedures in order to prevent data loss that might occur from a power failure.
- Alternate, or “hot” sites. Some organizations choose to have an alternate site where an exact replica of their critical data is always kept up to date. When the primary site goes down, the alternate site is immediately brought online so that little or no downtime is experienced.
As information has become a strategic asset, a whole industry has sprung up around the technologies necessary for implementing a proper backup strategy. A company can contract with a service provider to back up all of their data or they can purchase large amounts of online storage space and do it themselves. Technologies such as Storage Area Networks (SAN) and archival systems are now used by most large businesses for data backup.
“Chapter 6: Information Systems Security” from Information Systems for Business and Beyond (2019) by David Bourgeois is licensed under a Creative Commons Attribution-NonCommercial 4.0 International License, except where otherwise noted.